Introduction
A TTS veteran, David joined the company while completing his Management Information Systems degree at the University of Central Florida (UCF). David became a senior controls engineer in the TTS organization and has an extensive history working on the design, programming, installation, and commissioning of gas turbine control systems for power and pipeline applications. David completed his MBA at UCF in 2021 and was promoted to Business Development Manager. David now works to help expand TTS’s Power Generation customer base and will work to develop new product and service offerings for this market. David’s Cyber Security background starts with CCNA education early in his career and has been compounded by 16 years of industry experience. Recently, David completed UCF’s Cybersecurity defense program and is working on his Certified Information Systems Security Professional (CISSP) cert.
Question 1: What are the leading factors driving the need for a control system upgrade?
Operating System Obsolescence: this is a big one. As I’ll note later, industrial software companies are still playing catch-up. As many know (at least, I hope they do!) Windows 7, one of the most popular Operating Systems in modern controls, had its support terminated by Microsoft on January 14, 2020. That means, in short, that security patching will no longer be done by Microsoft. This means that many current systems still in operation do not have any patching and could be compromised by an attacker with relative ease. Windows 10 (Home and Pro), popular for more recent installations, will end its support on October 14, 2025. (1)
The obsolescence of operating systems comes with a few consequences:
- Unavailability of replacement hardware/software – say a customer has a Windows 7 HMI Workstation and they experience a computer failure – replacing this system is not as easy as going back to the Workstation OEM (Dell, HP, Lenovo, etc.) and ordering a new machine. Since machines are no longer sold with Windows 7, the list of replacement options is becoming smaller over time.
- Using the above example, the customer may have an over-arching IT policy requiring all new PC’s to be specified and procured by IT. Now suppose they’ve specified a cutting-edge machine with the latest Windows 11. It is almost guaranteed that the HMI software (or other applications) will not be compatible with the new operating system.
I’ve seen a lot of activity in this area – customers forced into tough decisions: Do they upgrade their entire system to comply in all areas, or do they save their precious budgets and keep things as-is? With tightening budgets from management, the solution isn’t always cut and dry. The answer lies somewhere in between. In our experience, customers will opt to do upgrades in stages: minimize downtime, and maximize security.
Agreement with IT policies
Many sites are grappling with the impact of IT (Information Technology) departments that have very little experience with OT (Operational Technology). OT has always been focused on connectivity: being able to place monitoring devices anywhere, connecting your remote SCADA system via Modbus TCP, or having an application accessing data via OPC for data collection. IT has concerns that are focused on things like zero-trust, multi-factor authentication, etc. These focuses don’t always agree, and this conflict can provide a lot of challenges for companies of all sizes. In most cases, this push from IT can result in plants needing to quickly modify control systems or operator interfaces to be compliant with modern standards.
Agreement with NERC-CIP requirements
NERC (North American Reliability Corporation) is a non-profit entity that has been designated by FERC (Federal Electric Reliability Commission) to take the role of a national ERO (Electric Reliability Organization). As mentioned above, the reasons for modifying a control system might be that a plant has fallen under the classification of a “Critical Asset” by NERC. These regulations can often be complicated to understand, and as a result, many consulting businesses have grown to assist in this area.
Question 2: What major sections of the control system(s) are vulnerable to cyber security threats, and how?
- Operator Workstations- Any device connected to a network or even isolated devices with USB ports can become the victim of an attack. Therefore, it is necessary to understand the threats a plant faces and plan their security accordingly. This stems from good practices by employees while also actively maintaining security patching and appropriate isolation from external systems.
- PLCs (Programmable Logic Controllers), or PACs (Programmable Automation Controllers), have the capability of dismantling a specific process that could exist in the wild. Personnel – As I’ll note later, an organizational Cybersecurity-aware culture is as essential for protecting your assets as any piece of the fancy security appliance. Educating your workforce can prevent employees from circumventing security measures and being more aware of attacks such as “phishing.”
Question 3: What should a client look for in a vendor when selecting a control system retrofit/upgrade?
Evidence of strict adherence to cybersecurity policies in the vendor’s internal organization: Good practices start at home. If your vendor practices good security, you can count on them to provide you with a secure system. However, it is important to note that security isn’t absolute – meaning a secure system design can only take you so far. Security is ever-changing and requires continuous vigilance to maintain. There are many anecdotes I could use here, but one that comes to mind is: Imagine owning a car and taking it to the dealership for service. How much more likely would you be to buy a car from that dealership if you had a positive service experience? It seems like common sense, but a glimpse behind the scenes, or “under the hood,” if you will, can be very telling for future experiences.
Question 4: What’s a common oversight by organizations regarding Cybersecurity?
Cybersecurity has a surprising number of parallels with personnel safety. You wouldn’t work with an organization that was unsafe or that didn’t have safety policies and a safe work culture. A large majority of Cybersecurity is simply awareness: is the link I’m clicking in my email safe? (In parallel, is the ladder I’m about to climb safe? Do I have the proper PPE to complete this task?) The human attack vector is the biggest wildcard in Cybersecurity. You can have the best patching systems, the latest next-gen firewalls, etc., yet a seemingly simple act by a user accessing a nefarious link can wreak havoc. Having a safety culture as well as a cybersecurity culture at a modern organization is important to the prevention of damaging important company assets.
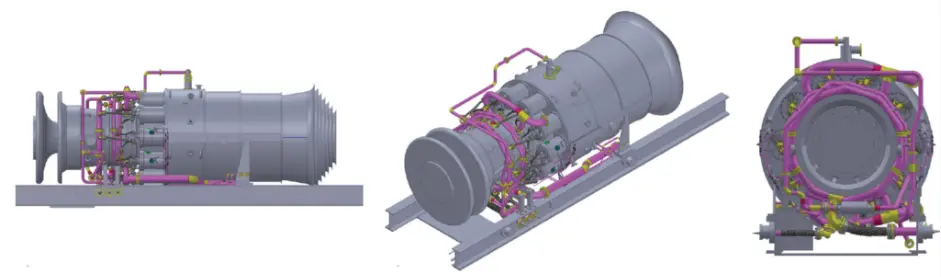
About TTS
TTS Energy Services (TTS) is the corporate parent for TTS Power and TTS Midstream. TTS provides engineering and construction expertise for the energy industry worldwide. The company’s long history and experience in providing technical solutions to global energy entities make it a leader in its field. TTS has successfully managed numerous power and compressor station modernization projects and supplied innovative and unique engineering solutions to challenging problems for their energy customers. Since 1983, TTS’s leadership and engineering teams have provided innovative technologies and engineered high-value solutions to over 450 clients worldwide.